Windows 10 → 11 Migration
The largest migration wave in a decade. End of support deadlines force organizations to move thousands of devices — each with application configurations that must survive the OS transition.
VDI Rollout Enterprise
Non-persistent VDI environments reset to a golden image after every session. Application customizations must be captured at session end and restored at next login. The CLI integrates with login/logoff scripts to automate the cycle.
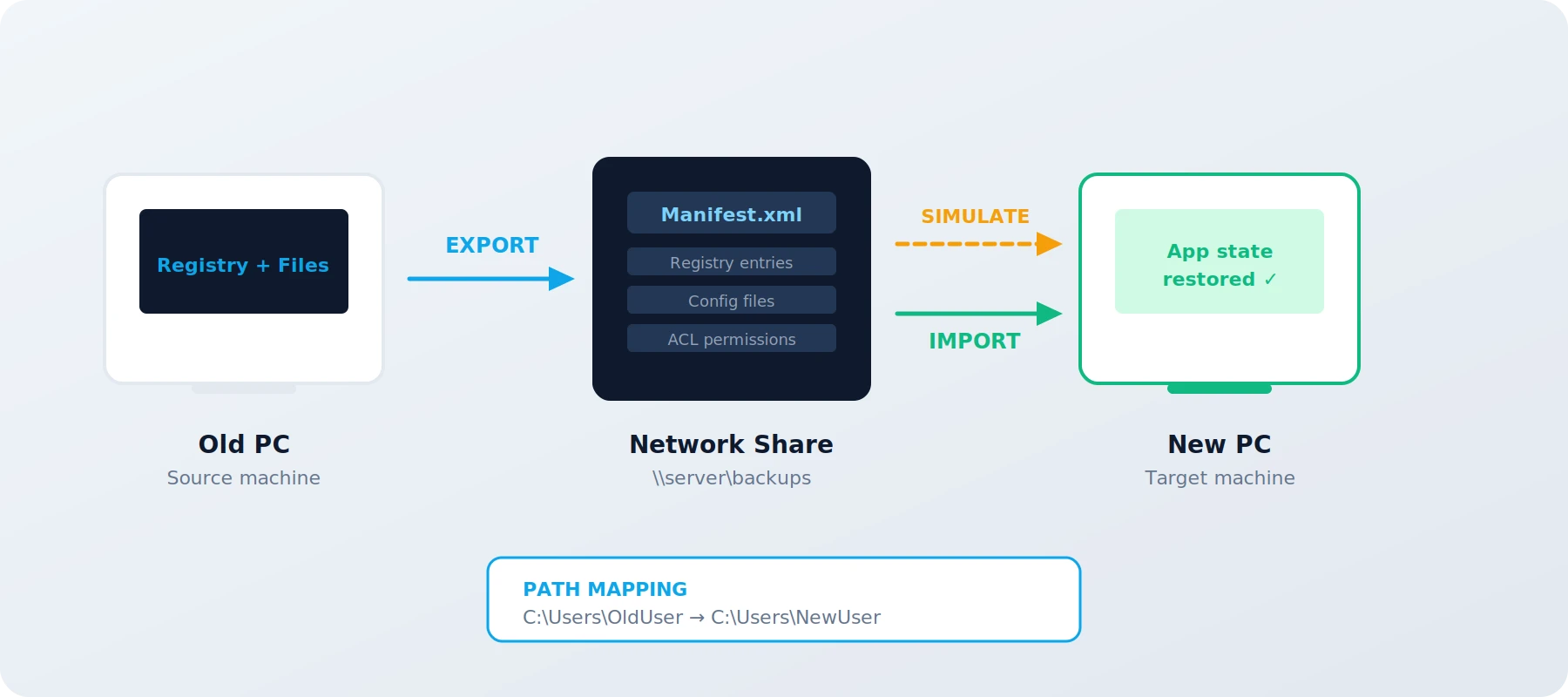
Workflow: Export at logoff via CLI → store manifest on network share → VDI resets to golden image → import at login via CLI. Fully automated, no user interaction.
Key capability: UNC network share support with Credential Manager integration for unattended Scheduled Task operation.
Staged Migration
Large rollouts run in waves. Wave 1 validates the process on a small batch. Simulation mode on the first wave catches mapping issues before they multiply across hundreds of devices.
GUI workflow: Export from reference machines → simulate on Wave 1 → review diff report → adjust mappings → import via GUI on subsequent waves.
Enterprise workflow: Deploy to Wave 2–N via CLI with SCCM/Intune/MDT. Preflight validation (--preflight --import) as a pipeline gate before each wave. Enterprise
Zero Data Loss
The combination of manifest-driven scope, simulation-before-import, and hash-chained audit logging creates a verifiable chain from source to target. Every registry key, file, and ACL change is documented and traceable.
Evidence: Diff CSV shows exactly what changed. Local audit log records who did it, when, and from which machine. Enterprise adds automated Compliance Reports and SIEM forwarding for centralized audit.
Rollback: System restore point created automatically before import. Rollback to the pre-import state is one step away.
Cost comparison: 250 devices, 8 apps each
Manual / Scripts
| Script preparation & testing | 40 h × 85 € | 3,400 € |
| Manual config per device (45 min) | 187 h × 85 € | 15,937 € |
| Error correction (~15%) | 19 h × 85 € | 1,615 € |
| Support tickets (week 1–2) | 20 h × 85 € | 1,700 € |
| Total | 22,650 € | |
With AppProfileSafe Enterprise
| App definitions (one-time) | 4 h × 85 € | 340 € |
| Import + mapping (5 min/device) | 21 h × 85 € | 1,785 € |
| Error correction (~2%) | 1.3 h × 85 € | 106 € |
| Enterprise license (250 devices, Tier S) | 250 × 18 € | 4,500 € |
| Total | 6,731 € | |
Cost comparison uses Enterprise edition with CLI automation. Community Edition reduces the license cost to zero — manual GUI operations take slightly longer per device but require no license.