Verify every precondition before execution
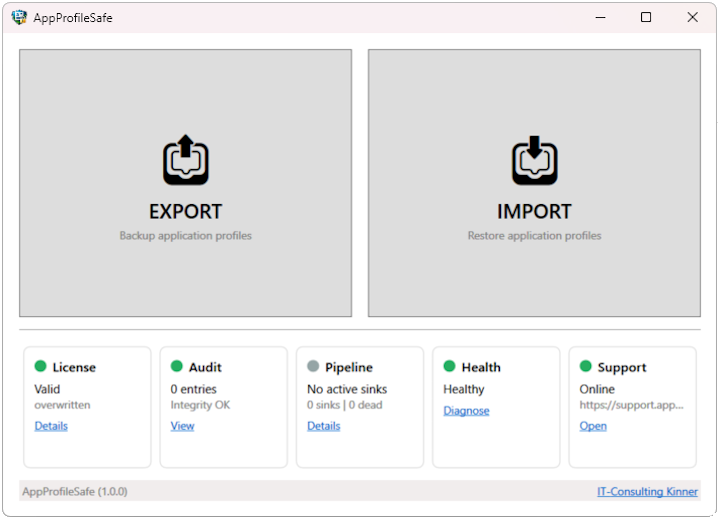
The preflight system validates the execution environment before any export or import begins. In the GUI, preflight runs automatically before every operation. Enterprise adds CLI preflight with structured JSON reports for deployment pipeline gates.
Environment Checks
Preflight validates the execution environment before any data operation. Checks include manifest path accessibility, app definition schema compliance, disk space availability, and audit log integrity.
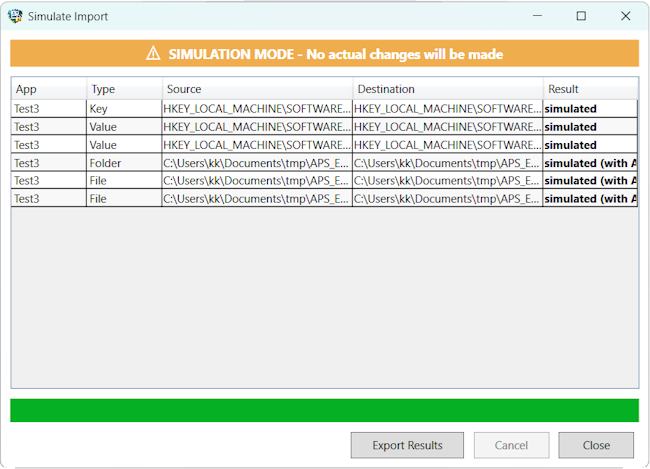
GUI integration: Health dashboard tiles show real-time status for License, Audit, and Health. Issues are visible before the user opens the export or import dialog. Preflight runs automatically before every operation.
CLI integration: --preflight --export or --preflight --import runs all checks and exits with a structured JSON report. Non-zero exit code if any check fails. Designed for deployment pipeline gates. Enterprise
- Manifest path existence and write access
- App definition XSD schema validation
- Disk space estimation and validation
- Audit log integrity (hash chain verification)
- License validation (Enterprise: feature flags and expiry)
- SIEM endpoint connectivity Enterprise
Disk Validation
Before export, preflight estimates the required disk space based on the app definitions and checks available space on the target volume. Before import, it validates space on the volumes where registry hives and file targets reside.
Export check: Estimates total size from defined registry scope and file paths. Compares against available space on the manifest target volume (local or UNC).
Import check: Validates available space on the system volume (registry) and all target file system volumes. Accounts for ACL metadata overhead.
Permission Checks
Preflight verifies write access to target paths before the operation begins. For export, it confirms the manifest directory is writable. For import, it checks write access to target registry keys and file directories — catching permission issues before any changes are attempted.
Registry: Verifies write access to target hives and keys. Reports specific keys where access is denied.
File system: Tests write access to target directories. Reports inaccessible paths with the underlying Windows error code.