Tamper-evident logging with cryptographic verification
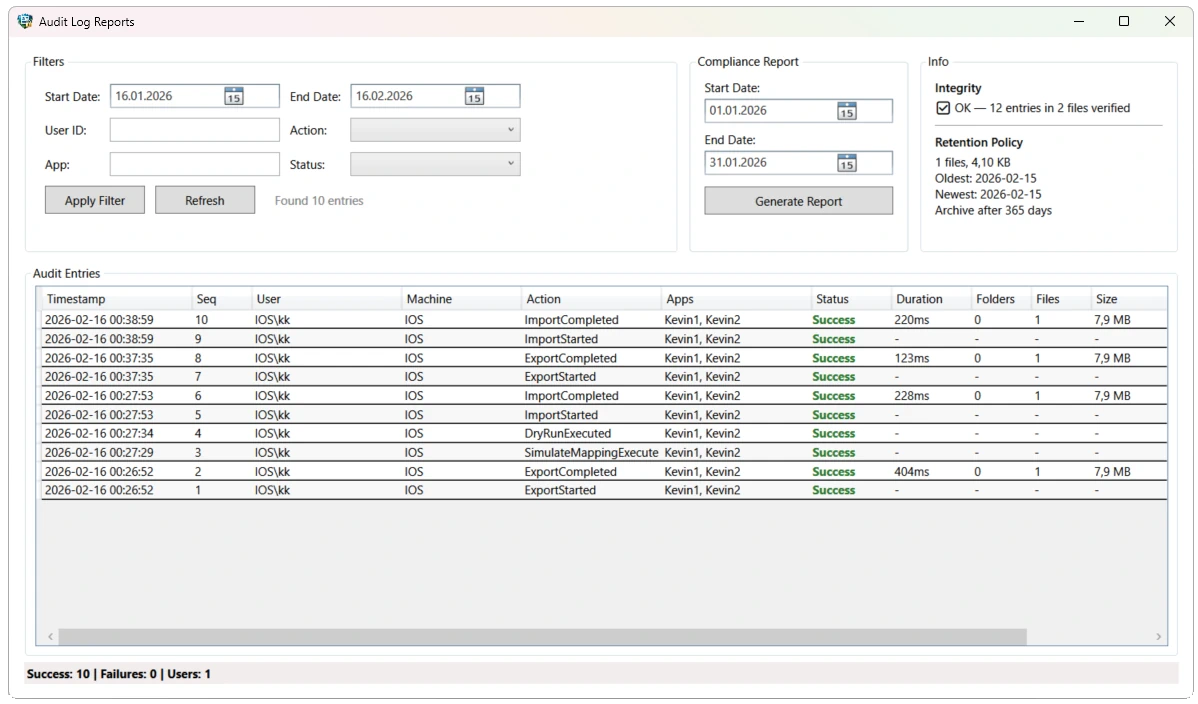
The audit log is a hash-chained CSV where each entry’s HMAC depends on the previous entry. Any modification, deletion, or reordering of entries breaks the chain and is detected on the next integrity check. Included in all editions.
AuditIntegrityService
The integrity service verifies the complete audit trail on every application startup. It reads all audit CSV files in chronological order, checks sequence number continuity, and validates that each entry’s PreviousHash matches the preceding entry’s EntryHash.
Hash chain: Each entry is HMAC-SHA256 signed using a key stored in Windows Credential Manager. The hash covers timestamp, sequence number, user, action, target, and success status. Fallback to unsigned SHA-256 if no HMAC key is available.
Startup check: Integrity verification runs automatically in both Community and Enterprise editions. In Enterprise, failures are additionally dispatched as Critical severity events to SIEM.
- Chronological file processing (audit_yyyy-MM.csv)
- Sequence gap detection across monthly file boundaries
- Hash chain continuity verification (PreviousHash == EntryHash[n-1])
- HMAC key stored in Windows Credential Manager
- Integrity failures visible in Audit Log Viewer (all editions)
- Integrity failures dispatched as Critical events to SIEM Enterprise
Tamper Detection
The hash chain design means that modifying any single entry invalidates all subsequent entries. Deleting an entry creates a sequence gap. Inserting an entry breaks the hash chain. Reordering entries breaks both sequence and chain.
Detection scope: Entry modification, entry deletion, entry insertion, entry reordering, and diff CSV tampering (DiffHash= in Details field verified separately).
Retention Policies
The AuditRetentionService manages log lifecycle with configurable retention periods. Logs past the retention window are either archived to a separate path (with a LogArchived audit entry recording the last hash and sequence) or deleted. Associated diff CSV files are cleaned up automatically.
Archival audit trail: When a log file is archived, the archival operation itself is recorded in the active audit log with the archived file’s last sequence number and hash — maintaining chain of custody.