Extract, transport, restore — with full fidelity
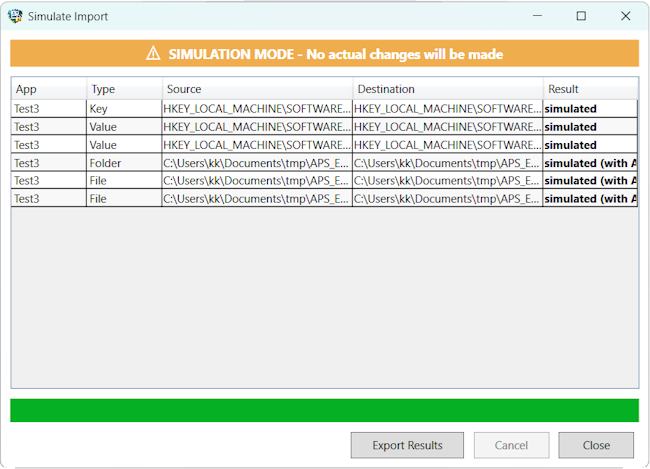
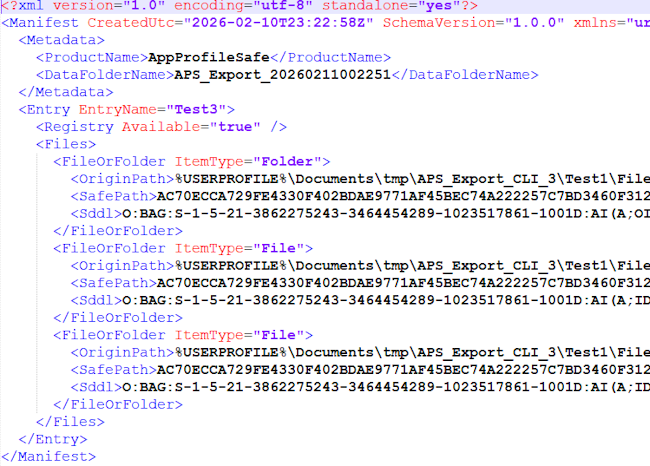
The migration engine captures application state from the registry, file system, and NTFS security layer. Data is written atomically and validated against XSD schemas before commit.
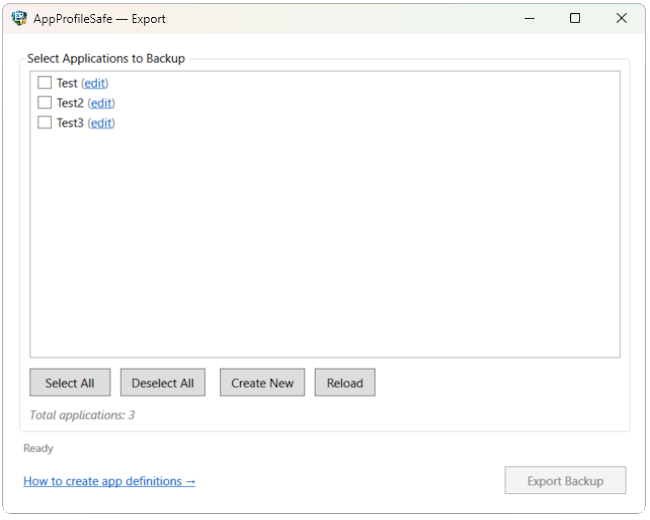
Registry Extraction
Exports full keys or individual values from any supported hive. All native data types are preserved — REG_SZ, DWORD, QWORD, BINARY, MULTI_SZ, EXPAND_SZ. Protected keys are logged and skipped without aborting the operation.
Scope control: App definitions specify per-key or per-value targets. Only what is defined gets exported — no hive-wide snapshots, no accidental captures.
Resilience: Access-denied on protected keys is logged with full detail but never aborts the export. Remaining entries continue normally.
- All hives: HKCU, HKLM, HKCR, HKU, HKCC
- Per-value or per-key scope in app definitions
- XML serialization validated against RegistrySchema XSD
- Protected keys logged with access-denied detail, never fatal
File System Extraction
Backs up application files and folders with recursive traversal or single-file targeting. Paths use environment variables for portability across machines. The manifest records file hashes and sizes for downstream diff comparison.
Portability: Paths are stored with environment variables (%APPDATA%, %LOCALAPPDATA%, %USERPROFILE%, %PROGRAMDATA%) and expanded at import time on the target machine.
Manifest tracking: Each entry records DataFolderName, content hash (SHA256), and file size. The dry run engine uses these for change detection.
- Recursive folder backup or individual file selection
- Environment variables expanded at import time for portability
- Content hashing (SHA256) for dry run and integrity verification
- Manifest records DataFolderName for portable export packages
ACL Preservation
NTFS security descriptors are captured during export using AccessControlSections.All and restored during import. Existing files receive additive ACL merges; new files get the full descriptor.
Consistency: Export and dry run both read AccessControlSections.All for comparison. Import applies .Access for existing files (additive merge) and .All for new files.
Atomic Writes
All file operations use a write-to-temp, then atomic-move pattern. If the process is interrupted mid-write, the target file is never left in a partial state.
Implementation: AtomicFileWriter writes to a temporary file in the same directory, then calls File.Move with overwrite. The event queue store uses the same pattern.
Path Guard
Before any write operation, the import engine validates that target paths are within expected boundaries. Entries referencing paths outside the application scope are rejected.
What it catches: Mapping rules that accidentally rewrite to system directories. Manifest entries with absolute paths that bypass environment variable expansion.